The problem
1. I had an encrypted Time Machine backup which was not used for months2. This backup was not on an official Apple Time Capsule or on a USB HDD, but on a WD MyCloud NAS
3. I needed files from this backup
4. After running out of time I only had SSH access to the macOS, no GUI
The struggle
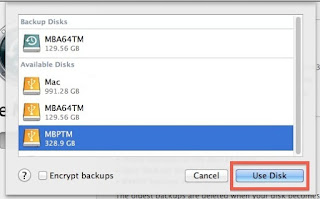
By default, Time Machine is one of the best and easiest backup solution I have seen. As long as you stick to the default use case, where you have one active backup disk, life is pink and happy. But this was not my case.As always, I started to Google what shall I do. One of the first options recommended that I add the backup disk to Time Machine, and it will automagically show the backup snapshots from the old backup. Instead of this, it did not show the old snapshots but started to create a new backup. Panic button has been pressed, backup canceled, back to Google.
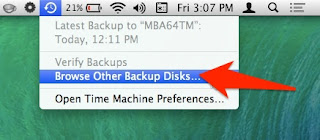
Other tutorials recommend to click on the Time Machine icon and pressing alt (Option) key, where I can choose "Browse other backup disks". But this did not list the old Time Machine backup. It did list the backup when selecting disks in Time Machine preferences, but I already tried and failed that way.
YAT (yet another tutorial) recommended to SSH into the NAS, and browse the backup disk, as it is just a simple directory where I can see all the files. But all the files inside where just a bunch of nonsense, no real directory structure.
YAT (yet another tutorial) recommended that I can just easily browse the content of the backup from the Finder by double-clicking on the sparse bundle file. After clicking on it, I can see the disk image on the left part of the Finder, attached as a new disk.
Well, this is true, but because of some bug, when you connect to the Time Capsule, you don't see the sparse bundle file. And I got inconsistent results, for the WD NAS, double-clicking on the sparse bundle did nothing. For the Time Capsule, it did work.
At this point, I had to leave the location where the backup was present, and I only had remote SSH access. You know, if you can't solve a problem, let's complicate things by restrict yourself in solutions.
Finally, I tried to check out some data forensics blogs, and besides some expensive tools, I could find the solution.
The solution
Finally, a blog post provided the real solution - hdiutil.The best part of hdiutil is that you can provide the read-only flag to it. This can be very awesome when it comes to forensics acquisition.
To mount any NAS via SMB:
mount_smbfs afp://<username>@<NAS_IP>/<Share_for_backup> /<mountpoint>
To mount a Time Capsule share via AFP:
mount_afp afp://any_username:password@<Time_Capsule_IP>/<Share_for_backup> /<mountpoint>
And finally this command should do the job:
hdiutil attach test.sparsebundle -readonly
It is nice that you can provide read-only parameter.
If the backup was encrypted and you don't want to provide the password in a password prompt, use the following:
printf '%s' 'CorrectHorseBatteryStaple' | hdiutil attach test.sparsebundle -stdinpass -readonly
Note: if you receive the error "resource temporarily unavailable", probably another machine is backing up to the device
And now, you can find your backup disk under /Volumes. Happy restoring!
Probably it would have been quicker to either enable the remote GUI, or to physically travel to the system and login locally, but that would spoil the fun.
More information
- Pentest Tools Github
- Tools For Hacker
- Nsa Hack Tools Download
- Underground Hacker Sites
- Termux Hacking Tools 2019
- Hack Website Online Tool
- Pentest Tools Subdomain
- Hacker Tools List
- Hack Tools
- Hacker Techniques Tools And Incident Handling
- Nsa Hack Tools Download
- Pentest Tools Alternative
- Pentest Tools Android
- Hack Tools Github
- Install Pentest Tools Ubuntu
- What Are Hacking Tools
- Pentest Tools Website Vulnerability
- Pentest Tools Android
- Hack Tools
- Hacking Tools Windows
- Hacker Tool Kit
- Top Pentest Tools
- World No 1 Hacker Software
- Hacker Tools Windows
- Hacking Tools For Beginners
- Pentest Tools For Android
- Hack App
- Pentest Tools Free
- Hacker Tools
- Pentest Tools Alternative
- Hacking Tools For Mac
- New Hacker Tools
- Black Hat Hacker Tools
- Hack Rom Tools
- Ethical Hacker Tools
- Android Hack Tools Github
- Github Hacking Tools
- Pentest Tools Bluekeep
- Hacking Tools Windows
- Pentest Tools Online
- Pentest Tools Port Scanner
- Hacker Tools Windows
- Pentest Reporting Tools
- Pentest Tools Apk
- Pentest Reporting Tools
- What Are Hacking Tools
- Tools 4 Hack
- Hack Tools For Pc
- Hacker Tools Linux
- Hacking Tools Pc
- Hacker Tools Online
- Hacking Tools Pc


No comments:
Post a Comment